printer hacking 101 walkthrough ( tryhackme.com )
WALKTHROUGH (spoiler) OF PRINTER HACKING 101 by swafox in Try Hack Me (tryhackme.com)
Unit 1 introduction
In This section the creator of the room shared some quick info about the famous Pewdiepie hacking. Where the hacker hacked about 50,000 printers and printed a page asking for subscribing to pewdiepie youtube channel 😊
Unit 2 ipp port
The cause of pewdiepie hacking was the open IPP port.
An open IPP port can expose a lot of sensitive information such as printer name, location, model, firmware version, or even printer wifi SSID.
What port does IPP run on?
631
Unit 3# Targeting and exploitation
In this section we have the deploy button to Deploy the machine
A handy tool for printer exploitation is shared.
Github: https://github.com/RUB-NDS/PRET
The Printer Exploitation Toolkit is a handy tool that is used for both local targeting and exploitation.
There are exactly three options you need to try when exploiting a printer using PRET:
1. ps (Postscript)
2. pjl (Printer Job Language)
3. pcl (Printer Command Language)
You need to try out all three languages just to see which one is going to be understood by the printer.
A nice cheat sheet: hacking-printers.net/wiki/index.php/Printer_Security_Testing_Cheat_Sheet
How would a simple printer TCP DoS attack look as a one-line command?
while true; do nc printer 9100; done
Review the cheat sheet provided in the task reading above. What attack are printers often vulnerable to which involves sending more and more information until a pre-allocated buffer size is surpassed?
Buffer Overflow
Now we need to get access of the system and use the printer.
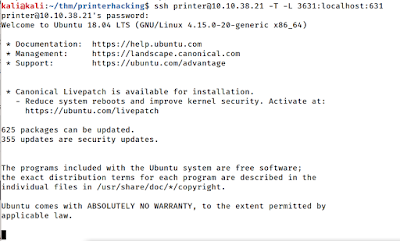
We will brute force the ssh for password. The username (printer) is given in the local tunneling command.
Hydra -l printer -P /usr/share/wordlists/rockyou.txt MACHINE_IP ssh
Once we have the password we will do a local tunneling to access the cups server on port 631 on our local port 3631, for this the following command will be used.
ssh printer@MACHINE_IP -T -L 3631:localhost:631
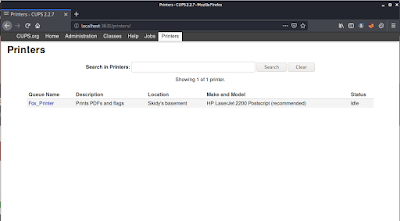
After the local tunnel is created. We will connect to the cups server on vulnerable machine by browsing localhost:3631
Going to the Printers section, we will find the Fox_Printer and it will give us the answer to the location of the printer.
Connect to the printer per the instructions above. Where's the Fox_Printer located?
Skidy's basement
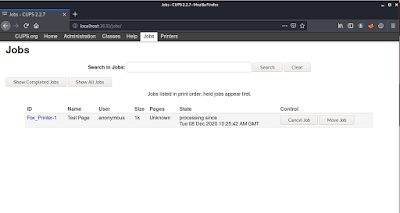
In order to find the size of the test page, go to the Fox_printer, and print a test page, then goto Jobs section , the test page file size will be mentioned.
What is the size of a test sheet?
1k



Comments